Imagine booking a flight online and seeing ticket prices from multiple airlines appear instantly in one place. Behind the scenes, those airlines’ systems are sharing data with the travel site in real time. Without a standard way to communicate, this kind of seamless experience would be chaotic, slow, and insecure. Modern apps constantly exchange information, and they need a reliable method to do it. That’s where Application Programming Interfaces, or APIs, come in—the universal translators and secure messengers of the digital world. In this guide, we’ll break down how APIs work exactly, using clear analogies and real-world examples that cut through the jargon.
The API Request-Response Cycle: A Waiter at Your Service
The first time I truly understood APIs, I wasn’t staring at code. I was waiting for pasta. The restaurant was slammed, orders flying, waiters weaving between tables like multiplayer characters in a boss battle. And it clicked: this is how APIs work.
Think of the diner as the client (your app). You’re hungry, so you place an order. The waiter is the API. The kitchen? That’s the server where the real work happens. You never step into the kitchen—you just trust the waiter to handle it. (And yes, sometimes you wonder what’s taking so long.)
Breaking Down the Request
Every API request has three core parts:
- Endpoint: The specific destination—like the exact table or kitchen station the waiter goes to.
- Method: What you want done. GET (retrieve data), POST (create something new), PUT (update it), or DELETE (remove it).
- Headers: Special instructions—dietary restrictions, VIP passes, or authentication tokens proving you’re allowed to order.
Pro tip: Authentication headers often carry API keys or tokens—without them, you’ll get turned away at the door.
Understanding the Response
Once the kitchen finishes, the waiter returns with your meal—the response. It includes a status code: 200 OK means success, 404 Not Found means the dish (or resource) doesn’t exist, and 500 Internal Server Error means something broke in the kitchen.
The plate itself is the response body, usually served as JSON (JavaScript Object Notation). JSON is lightweight and human-readable—structured in key-value pairs like { "order": "pasta" }. It’s become the standard because it’s simple, fast to parse, and language-agnostic (even if it looks deceptively plain).
Exploring the Blueprints: Common API Architectures and Protocols
When discussing how APIs work, it helps to understand the blueprints behind them. Not all APIs are built the same—and in my experience, choosing the right architecture feels a bit like choosing between a food truck, a formal banquet, or an à‑la‑carte café.
REST APIs (Representational State Transfer)
First, there’s REST—the undisputed workhorse of the modern web. REST follows three core principles: statelessness (each request contains all necessary information), client-server separation (frontend and backend operate independently), and the use of standard HTTP methods like GET and POST. Because it’s lightweight and flexible, REST dominates public web services (Fielding, 2000).
Some critics argue REST can lead to “over-fetching,” where clients receive more data than needed. That’s fair. Still, for most applications, its simplicity outweighs the inefficiency (and simplicity scales surprisingly well).
SOAP APIs (Simple Object Access Protocol)
On the other hand, SOAP feels almost archival. It relies heavily on XML and strict standards enforced through formal contracts (W3C, 2007). While many developers see it as rigid, I think that rigidity is its strength. Financial systems and enterprise platforms still rely on SOAP for high-security transactions. In environments where compliance is king, predictability wins.
GraphQL
Then comes GraphQL—the modern minimalist. Instead of a fixed menu like REST, it’s à‑la‑carte. Clients request exactly what they need—no more, no less (Facebook Engineering, 2015). This reduces over-fetching and improves efficiency.
| Architecture | Flexibility | Data Efficiency | Best Use Case |
|————–|————|—————–|—————|
| REST | High | Moderate | Public web apps |
| SOAP | Low | Structured | Enterprise security |
| GraphQL | Very High | High | Dynamic apps |
If security is your concern, revisit the fundamentals of data encryption explained clearly. Ultimately, no architecture is universally superior—only context decides.
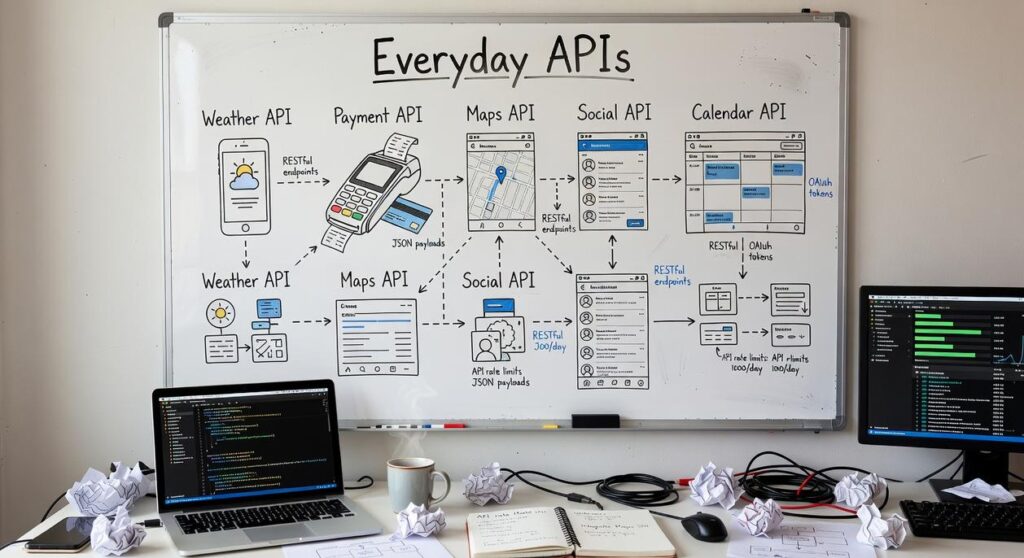
APIs in the Wild: Everyday Examples You Already Use

APIs (Application Programming Interfaces) are rulebooks that let two software systems talk securely and predictably. If that sounds abstract, consider this: more than 1 billion people use “Login with Google” each month, powered by OAuth, an authorization standard adopted by major platforms worldwide (Google Transparency Report). Instead of handing your password to every new app (yikes), OAuth issues a secure token that confirms your identity. In other words, the site verifies you without ever seeing your credentials. That’s not magic—that’s documented protocol design in action.
Social, Maps, and the Games You Play
Similarly, weather apps rely on services like the OpenWeather API, which processes millions of requests daily, to deliver real-time forecasts. Your map app? It likely embeds Google Maps APIs, which handle billions of monthly active users (Alphabet earnings reports). The app requests location data; the API returns coordinates, routes, and traffic overlays in milliseconds.
Meanwhile, online games constantly ping servers through APIs to sync player stats, inventory, and world state. When you unlock a new skin, that update travels through an API call. Smart home devices work the same way—your thermostat sends data to a cloud API, which responds with updated settings.
If you’ve ever wondered how APIs work in the section once exactly as it is given, the answer is simple: request, process, respond. Proven, scalable, everywhere.
A connected digital infrastructure separates leaders from laggards. In a siloed system (Platform A), teams rebuild features from scratch, updates crawl, and scaling feels like Jenga. In an API-driven model (Platform B), services plug into each other seamlessly, enabling innovation at speed. Think of the app economies around iOS and Android—APIs let developers extend core platforms without rewriting them.
Understanding how APIs work in the section once exactly as it is given clarifies why microservices outperform monoliths. Smaller services communicate via APIs, making updates safer and scaling cheaper. Critics argue monoliths are simpler. Short term, maybe. Long term, flexibility wins.
Harnessing the Power of Digital Connection
APIs are the connective tissue of the modern digital world, quietly powering the apps, platforms, and devices you rely on every day. They enable secure, standardized communication between different software systems, making seamless integration possible. By now, you’ve seen how APIs work exactly as it is given—through structured requests and precise responses that move data efficiently between systems.
Understanding APIs isn’t just for developers anymore. If you work with technology in any capacity, ignoring them means falling behind.
Don’t stay stuck in theory. Explore a public API like NASA’s or the Pokémon API today and watch the request-response cycle in action. Turn knowledge into skill—start experimenting now.

 Heathers Gillonuevo writes the kind of archived tech protocols content that people actually send to each other. Not because it's flashy or controversial, but because it's the sort of thing where you read it and immediately think of three people who need to see it. Heathers has a talent for identifying the questions that a lot of people have but haven't quite figured out how to articulate yet — and then answering them properly.
They covers a lot of ground: Archived Tech Protocols, Knowledge Vault, Emerging Hardware Trends, and plenty of adjacent territory that doesn't always get treated with the same seriousness. The consistency across all of it is a certain kind of respect for the reader. Heathers doesn't assume people are stupid, and they doesn't assume they know everything either. They writes for someone who is genuinely trying to figure something out — because that's usually who's actually reading. That assumption shapes everything from how they structures an explanation to how much background they includes before getting to the point.
Beyond the practical stuff, there's something in Heathers's writing that reflects a real investment in the subject — not performed enthusiasm, but the kind of sustained interest that produces insight over time. They has been paying attention to archived tech protocols long enough that they notices things a more casual observer would miss. That depth shows up in the work in ways that are hard to fake.
Heathers Gillonuevo writes the kind of archived tech protocols content that people actually send to each other. Not because it's flashy or controversial, but because it's the sort of thing where you read it and immediately think of three people who need to see it. Heathers has a talent for identifying the questions that a lot of people have but haven't quite figured out how to articulate yet — and then answering them properly.
They covers a lot of ground: Archived Tech Protocols, Knowledge Vault, Emerging Hardware Trends, and plenty of adjacent territory that doesn't always get treated with the same seriousness. The consistency across all of it is a certain kind of respect for the reader. Heathers doesn't assume people are stupid, and they doesn't assume they know everything either. They writes for someone who is genuinely trying to figure something out — because that's usually who's actually reading. That assumption shapes everything from how they structures an explanation to how much background they includes before getting to the point.
Beyond the practical stuff, there's something in Heathers's writing that reflects a real investment in the subject — not performed enthusiasm, but the kind of sustained interest that produces insight over time. They has been paying attention to archived tech protocols long enough that they notices things a more casual observer would miss. That depth shows up in the work in ways that are hard to fake.