Cyber threats have evolved into coordinated, persistent campaigns that probe the very foundation of your technology stack. If you’re searching for a way to truly secure your systems—not just patch vulnerabilities—you’re in the right place. This guide delivers a comprehensive, multi-layered blueprint for digital infrastructure cybersecurity, moving beyond surface-level fixes to address hardware, network, and system-level risks. Drawing on established security protocols and emerging hardware-based defenses, we outline a systematic approach to hardening your environment from the ground up. You’ll learn how to eliminate weak links, reinforce critical layers, and build a resilient security posture designed to withstand modern, sophisticated attacks.
The Foundation: Securing the Physical and Hardware Layers
Most security conversations start with firewalls and endpoint software. That’s a mistake.
I learned this the hard way after overlooking a routine firmware update on a staging server. Everything looked fine—until a boot-level anomaly slipped past our monitoring tools. The culprit wasn’t malware in the OS. It was firmware. That experience reshaped how I think about digital infrastructure cybersecurity: the real foundation isn’t software. It’s silicon.
Beyond the Firewall
Physical hardware and firmware form the BASE LAYER of trust. If that layer is compromised, everything above it is suspect (like building a skyscraper on quicksand and hoping for the best).
Firmware Integrity starts with UEFI Secure Boot—technology that ensures only cryptographically signed software runs during startup. According to NIST SP 800-147, firmware protections are essential to preventing persistent rootkits that survive OS reinstalls. Skipping updates because “nothing’s broken” is how things actually break.
Hardware Supply Chain Verification is another overlooked risk. Counterfeit or pre-tampered components can enter systems before deployment. Mitigation strategies include:
- Vendor attestation and component provenance checks
- Randomized hardware audits
- Firmware hash validation before rollout
I once trusted a “certified” reseller without verification. That shortcut cost weeks of forensic review.
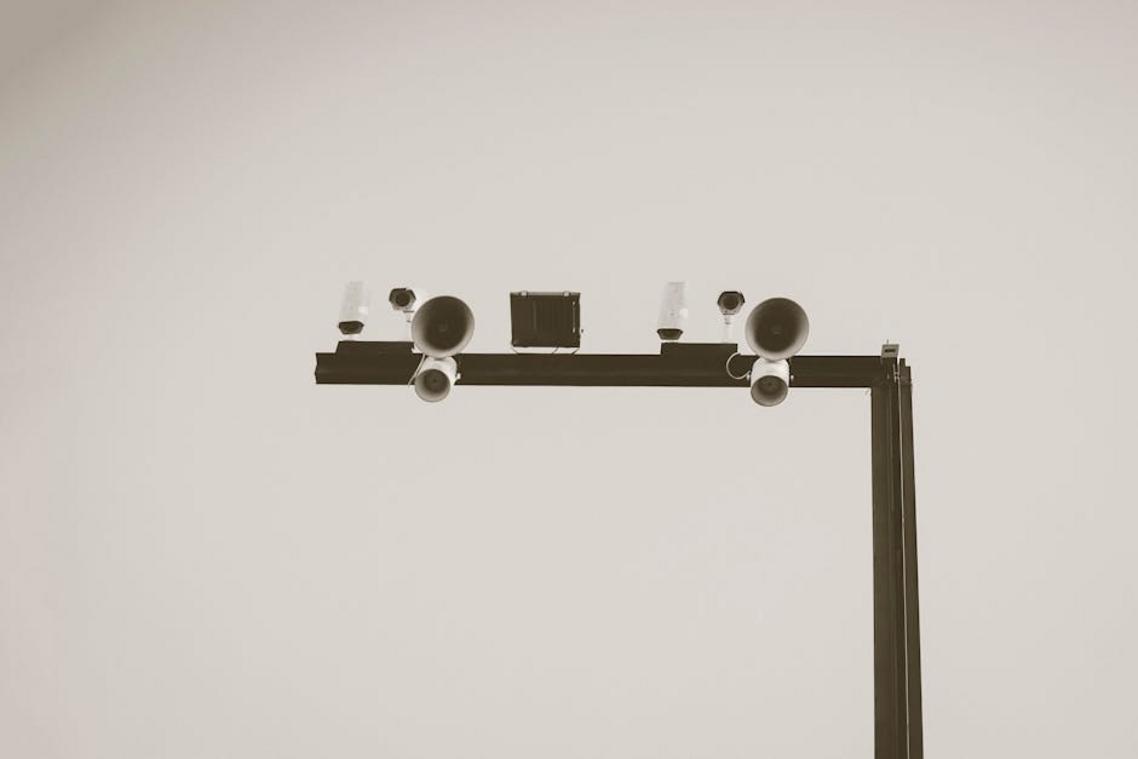
Finally, Physical Access Control matters more than many admit. If someone can touch your servers, they can own them. Badge logs, biometric checkpoints, and locked racks aren’t overkill—they’re table stakes.
Pro tip: treat server rooms like vaults, not storage closets.
The Network Perimeter: Your First Line of Digital Defense
A few years ago, I helped a small team recover from a ransomware scare that started with what looked like harmless traffic. That moment changed how I view the network perimeter. It’s not just a boundary; it’s the front door to everything you value.
To begin with, modern firewall strategy has evolved. Traditional firewalls relied on packet filtering (inspecting data packets based on IP addresses and ports). Today’s Next-Generation Firewalls (NGFWs) add deep packet inspection—analyzing the contents of traffic—and application awareness, meaning they can distinguish between legitimate app usage and malicious impersonation. It’s the difference between a bouncer checking IDs and one who actually knows the guest list.
However, even strong firewalls aren’t enough. That’s where network segmentation comes in. Segmentation divides a network into isolated zones, while microsegmentation applies that isolation at the workload level. In practice, when one server was compromised in a project I worked on, segmentation prevented lateral movement (a hacker’s favorite trick). The breach stopped there.
Next, IDS/IPS systems monitor traffic for known malicious patterns. Intrusion Detection Systems alert you; Intrusion Prevention Systems automatically block threats in real time. Think of them as motion sensors that don’t just beep—they lock the door.
Finally, Zero-Trust Network Architecture (ZTNA) shifts from “trust but verify” to “never trust, always verify.” Every request—internal or external—must authenticate continuously. In digital infrastructure cybersecurity, this mindset is no longer optional. It’s essential.
Hardening the Core: Application and Data Security Protocols
Security failures rarely happen because teams don’t care. They happen because someone assumes, “We’ll patch it next week.” I’ve made that mistake. Once, a delayed update on a staging server became the weak link that exposed production credentials (yes, staging matters). The lesson? Consistency beats urgency.
Systematic Patch Management
Patch management means creating an automated process to identify, test, and deploy updates across operating systems and applications. Automation tools like WSUS or configuration managers reduce human lag, which is often the real vulnerability. According to Verizon’s Data Breach Investigations Report, unpatched vulnerabilities remain a leading attack vector (Verizon DBIR). Pro tip: schedule maintenance windows that teams actually respect—otherwise patches quietly pile up.
Vulnerability Scanning and Penetration Testing
Vulnerability scanning uses automated tools to detect known weaknesses, while penetration testing simulates real-world attacks led by experts. Some argue scans alone are enough. They’re not. Automated tools find predictable flaws; human testers find logic gaps and misconfigurations (the “how did we miss that?” moments).
Principle of Least Privilege (PoLP)
The Principle of Least Privilege means granting users and services only the minimum access required. It sounds restrictive, and some teams resist it for convenience. But over-permissioned accounts are gold for attackers. Tight access controls are foundational to digital infrastructure cybersecurity.
Data Encryption in Transit and at Rest
Encryption protects confidentiality and integrity. TLS 1.3 secures data in motion; AES-256 safeguards stored data (NIST). Think of it as locking both the mailbox and the letters inside.
For broader architectural context, revisit understanding cloud native architecture in modern it environments.
The human layer is where security holds or collapses. Back in 2020, when remote work surged overnight, many teams learned that annual awareness videos were not enough. Real resilience comes from simple, repeatable protocols embedded in daily workflows, not a dusty checklist. That means mandatory multi-factor authentication across every critical system—no exceptions. MFA, or multi-factor authentication, requires two or more proofs of identity. It is STILL the most effective barrier against account takeover, according to CISA. After three months of phishing campaigns, click rates typically drop. Could your team pass today? Pro tip: treat digital infrastructure cybersecurity drills like fire drills.
Building a Proactive and Resilient Security Posture
You set out to build a stronger, smarter defense—and now you have a clear blueprint for protecting your systems from the silicon to the screen. digital infrastructure cybersecurity is only as strong as its weakest link. One overlooked firmware update or one untrained employee can open the door to a serious breach.
A layered, proactive approach ensures that if one control fails, the rest stand firm. That’s how you prevent disruption, data loss, and costly downtime.
Start now: audit your foundational hardware and physical security controls first. Close the gaps before attackers find them—and build resilience from the ground up.


 Heathers Gillonuevo writes the kind of archived tech protocols content that people actually send to each other. Not because it's flashy or controversial, but because it's the sort of thing where you read it and immediately think of three people who need to see it. Heathers has a talent for identifying the questions that a lot of people have but haven't quite figured out how to articulate yet — and then answering them properly.
They covers a lot of ground: Archived Tech Protocols, Knowledge Vault, Emerging Hardware Trends, and plenty of adjacent territory that doesn't always get treated with the same seriousness. The consistency across all of it is a certain kind of respect for the reader. Heathers doesn't assume people are stupid, and they doesn't assume they know everything either. They writes for someone who is genuinely trying to figure something out — because that's usually who's actually reading. That assumption shapes everything from how they structures an explanation to how much background they includes before getting to the point.
Beyond the practical stuff, there's something in Heathers's writing that reflects a real investment in the subject — not performed enthusiasm, but the kind of sustained interest that produces insight over time. They has been paying attention to archived tech protocols long enough that they notices things a more casual observer would miss. That depth shows up in the work in ways that are hard to fake.
Heathers Gillonuevo writes the kind of archived tech protocols content that people actually send to each other. Not because it's flashy or controversial, but because it's the sort of thing where you read it and immediately think of three people who need to see it. Heathers has a talent for identifying the questions that a lot of people have but haven't quite figured out how to articulate yet — and then answering them properly.
They covers a lot of ground: Archived Tech Protocols, Knowledge Vault, Emerging Hardware Trends, and plenty of adjacent territory that doesn't always get treated with the same seriousness. The consistency across all of it is a certain kind of respect for the reader. Heathers doesn't assume people are stupid, and they doesn't assume they know everything either. They writes for someone who is genuinely trying to figure something out — because that's usually who's actually reading. That assumption shapes everything from how they structures an explanation to how much background they includes before getting to the point.
Beyond the practical stuff, there's something in Heathers's writing that reflects a real investment in the subject — not performed enthusiasm, but the kind of sustained interest that produces insight over time. They has been paying attention to archived tech protocols long enough that they notices things a more casual observer would miss. That depth shows up in the work in ways that are hard to fake.